Overview
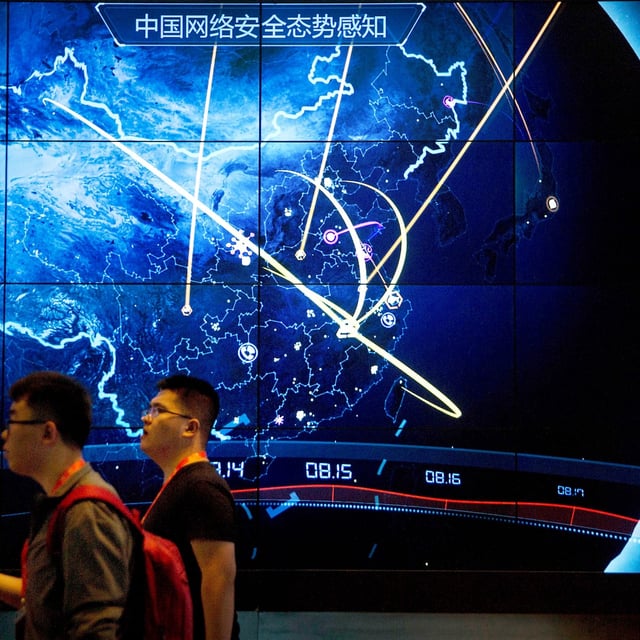
- A 37-page joint advisory from the FBI, NSA, CISA and 12 allied governments attributes a years-long campaign to the China-linked group known as Salt Typhoon and provides indicators of compromise and mitigations.
- Authorities said the operation touched at least 600 organizations across roughly 80 countries, including about 200 in the US, with notifications and investigations continuing.
- The advisory names three Chinese companies — Sichuan Juxinhe, Beijing Huanyu Tianqiong and Sichuan Zhixin Ruijie — as facilitators of the campaign, noting Juxinhe was sanctioned by the US Treasury in January.
- Intrusions targeted backbone and edge routers by exploiting known flaws in Cisco (CVE-2018-0171, CVE-2023-20198, CVE-2023-20273), Ivanti (CVE-2023-46805, CVE-2024-21887) and Palo Alto Networks (CVE-2024-3400), then modified routing and ACLs and created GRE or IPsec tunnels to persist and exfiltrate.
- Officials warn stolen data from telecom, lodging and transportation can enable tracking of targets’ communications and movements, as partners including the UK and the Netherlands validate parts of the findings and urge careful, coordinated threat hunting.