Overview
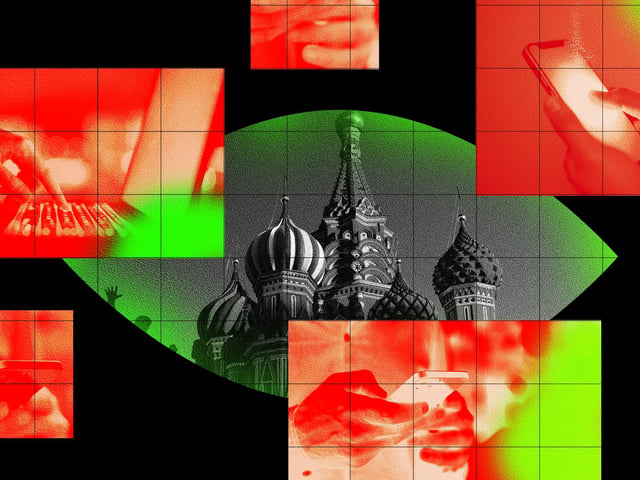
- Secret Blizzard, tied to FSB’s Center 16, likely leverages Russia’s SORM lawful intercept system to secure adversary-in-the-middle positions at the ISP level in Moscow.
- The group exploits captive portals on local ISPs to deploy ApolloShadow malware disguised as Kaspersky updates, tricking embassy staff into installing fraudulent root certificates.
- Once installed, ApolloShadow disables TLS encryption and redirects diplomatic devices to malicious domains, exposing credentials and browsing data in plaintext.
- Microsoft first detected the ISP-level intrusions in February 2025 but assesses the campaign has persisted since at least 2024 against an undisclosed number of foreign embassies.
- Microsoft urges embassies and other sensitive organizations to route traffic through VPNs or encrypted tunnels and enforce zero-trust controls to guard against ISP-level espionage.