Overview
- Google and Mandiant now advise treating any Drift integration as potentially compromised, with evidence of impacts beyond Salesforce including a very small number of Google Workspace email accounts.
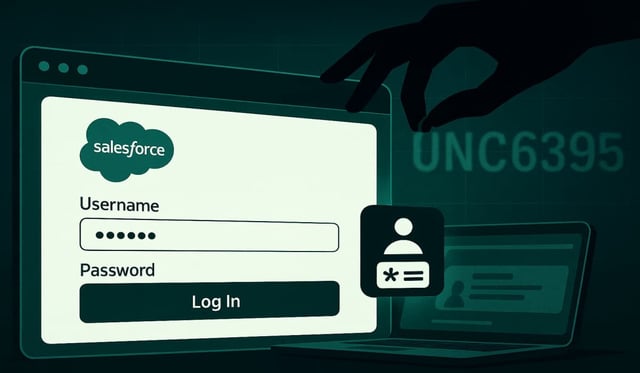
- The campaign, tracked as UNC6395, ran August 8–18 using stolen Drift OAuth and refresh tokens to query Salesforce objects and exfiltrate data at scale.
- GTIG estimates more than 700 organizations are potentially affected, though Salesforce maintains the core platform was not vulnerable and disabled the Drift connection.
- Salesloft confirmed broader exposure, removed Drift from AppExchange with Salesforce, and urged all Drift customers to revoke and rotate API keys and re‑authenticate integrations.
- Investigators report the actor searched exfiltrated data for secrets such as AWS access keys, VPN credentials, and Snowflake tokens, deleted query jobs to obscure activity, and used Tor and cloud hosting to mask infrastructure; ShinyHunters’ claim of responsibility remains unsubstantiated by Google.